Malware Overview
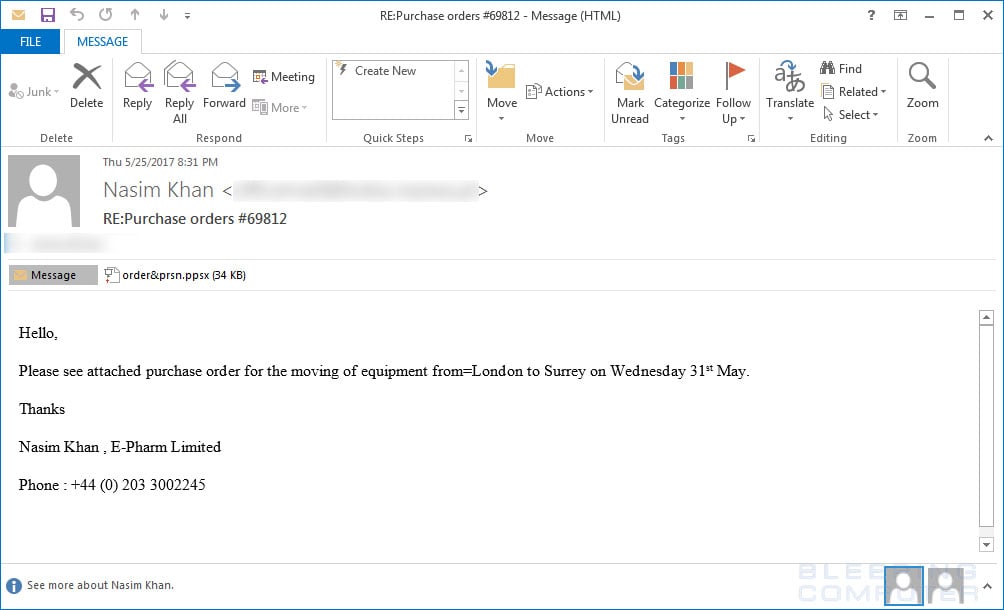
A newly discovered malware infection is masquerading in the form of a Microsoft PowerPoint file which downloads the infection as soon as users hover over a link. The file is named as “order&prsn.ppsx” or “order.ppsx” or “invoice.ppsx” and is sent as an attachment through email to victims with the subject line “RE:Purchase orders #69812” or “Fwd:Confirmation.
” The attachment may sometimes even contain zip files, which when extracted show the microsoft PowerPoint files. Security researchers have spotted a booby-trapped PowerPoint file that will download malware to a computer whenever a victim hovers over a link; no macro scripts are required.
PPSX files are identical to PPTX files, except they enter the PowerPoint presentational view when opened, instead of the PowerPoint edit mode. The Microsoft PowerPoint file contains only one slide with the following content, containing the linkified text “Loading…Please wait“.
Whenever the user hovers the URL, malicious code is executed that will invoke PowerShell and attempt to execute the following code.
![Malicious code [obfuscated]](https://www.bleepstatic.com/images/news/u/986406/Malware/PPSX-obfuscated-executed-command.jpg)
Protection against this Virus
Microsoft powerpoint files is aware of the malware and has said if users have Windows Defender and Office 365 Advanced Threat Protection activated, they will remove the malware by signaling a threat and closing down the file.
Contacted by Bleeping Computer, a Microsoft spokesperson provided more information on this attack vector.
Office Protected View is enabled by default and protects against the technique described in the report. Both Windows Defender and Office 365 Advanced Threat Protection also detect and remove the malware. We encourage users to practice good computing habits online, and exercise caution when enabling content or clicking on links to web pages. If the user is using an Office installation with the Protected View security feature enabled, Office will stop the attack from taking place.
As Microsoft powerpoint said in its statement, Office protects against this technique because Office Protected is enabled by default. Users and organizations that know they’ve turned off this feature should review their policy to take into consideration this attack vector.
Checkout our more services on Information and Cyber Security.




